Want to Learn More?: Transit Agencies Priorities for Cybersecurity
How Vendors Can Help Transit Improve Cybersecurity
The new study focuses on the role of vendors in cybersecurity and their relationships with the transit industry. Through detailed interviews and in-depth research, the team reported on several key findings.

Transit Agencies should integrate their cyber risk management program with their physical security risk management, creating a holistic Enterprise Risk Management program.
solarseven
In July 2022, the Mineta Transportation Institute (MTI) published a new report on cybersecurity for transit agencies. The report, entitled “Aligning Transit Agencies and Vendors in Face of Increasing Cyber Risk: Recommendation for Identifying and Addressing Cybersecurity Challenges,” examines the roles vendors play in the cybersecurity ecosystem and how transit agencies and their vendors can work together to address the challenges and threats posed by today’s cyber landscape. The report concludes with a series of recommendations for the various parties involved.
The MTI cyber research teams that included Scott Belcher, Brandon Thomas, Katie Seckman, Homayun Yaqub, Terri Belcher, and Eric Greenwald began their research in 2020 with the publication of “Is the Transit Industry Prepared for the Cyber Revolution? Policy Recommendations to Enhance Surface Transit Cyber Preparedness,” which revealed the transit industry was not well prepared to address the variety of cybersecurity threats that are now commonplace. The authors followed that foundational study with MTI White Papers on “Implications of the Sunburst Cybersecurity Attack on the Transit Industry;” “Will the Biden Administration’s ‘Made in America’ Executive Order Present Significant New Cybersecurity Obligations for Transit Operators?” and “Personal Data Protection as a Driver for Improved Cybersecurity Practices in U.S. Public Transit.”
The new study focuses on the role of vendors in cybersecurity and their relationships with the transit industry. Through detailed interviews and in-depth research, the team reported on several key findings.
First, there is a mismatch between the lifespan of physical transit equipment (upwards of 15 years) and the software and firmware that operates it. Transit agencies invest significant amounts of money in buses, trains, and other transit equipment, with the intention of keeping their passengers safe and ensuring reliability. Unfortunately, frequently they do not pay software maintenance agreements for the physical lifespan. The result being many functioning pieces of transit equipment have software that is out of date and are thus vulnerable to cyber threats.
Second, a considerable number of transit agencies have not learned how to effectively include cyber risk management policies and procedures in their procurement practices. Some do not include cyber requirements at all; while others require unnecessary, duplicative, or unachievable provisions that are not based on actual risk. This disconnect can lead to unnecessary costs and result in qualified vendors choosing not to bid.
Finally, the research revealed a lack of differentiation between “security” and “risk.” Security is the state of being free from or resilient to harm. Risk recognizes the constant exposure to threats and the need to manage them across the enterprise. Transit agencies and their vendors are never free from risk. Rather than seeking an unattainable state of total security. Agencies must shift to a position of managed risk. This involves accepting that the chance of exposure to harm is constant and unavoidable. It can be managed and mitigated, but not escaped. To do this, agencies must incorporate managing cyber risk into their recovery and response plans and into their agencies.
Based on these findings, the authors of the report made several recommendations:
Vendors should designate a security lead to help manage cyber risk. They should plan for periodic and independent security audits and penetration testing. Finally, vendors should engage in public-private security information forums to share information about cyber threats.
Transit Agencies should integrate their cyber risk management program with their physical security risk management, creating a holistic Enterprise Risk Management program. They should appoint a Chief Security Officer (CSO) to be responsible for physical and cyber security. An executive-level enterprise risk committee should be created and chaired by the CSO. Agencies should identify, evaluate, and manage end-of-life software and hardware to avoid lifecycle incongruities.
Associations should develop third-party risk management standards and incorporate them into templates for contract language, RFPs, and other artifacts for engaging with vendors. They should develop a comprehensive security questionnaire and assessment guide and minimum guidelines for cybersecurity audits, penetration tests, and other tools. Finally, they should provide guidance on investment in risk management.
The Department of Homeland Security (DHS) and U.S. Department of Transportation (U.S. DOT) should create a Sector Cybersecurity Executive with authority to establish cybersecurity guidance. They should update the 2015 Transportation Systems Sector Cybersecurity Framework Implementation Guidance to cover electric, connected, and autonomous vehicles.
The Federal Transit Administration (FTA) should require that transit procurements fund security maintenance; that transit agencies minimally meet the requirements in Transportation Security Administration (TSA) Security Directive 1582-21-01; and that transit CEOs to attest that their organization has met TSA-approved cybersecurity standards and completed an annual cybersecurity audit.
Congress should increase funding to DHS and U.S. DOT to develop and promulgate cybersecurity standards and increase formula grant funding to transit agencies, ensuring they can meet these cybersecurity standards.
The authors believe that implementation of these recommendations will improve cybersecurity for both transit agencies and their vendors, allowing a more efficient, safe working environment.
The full report is available here.
About the Authors: Scott Belcher and James Grimes are Research Associates, Mineta Transportation Institute, at San Jose State University.
More Security and Safety

LA Metro Sworn Officer Recruitment Draws 950 Applications on First Day
The California agency moves safety into its next phase, recruiting officers to help shape a transit-focused, community-centered force.
Read More →
FTA Plans Family-Friendly Transit Scorecard for Agencies Nationwide
The family-friendly transit dashboard is part of a broader effort by the FTA and U.S. Department of Transportation to increase transparency, accountability, and service quality across the nation's public transportation systems, said officials.
Read More →
New Public Safety Hub Opens in Downtown Houston
The substation strengthens METRO Police presence in an area where transit activity, pedestrian movement, and visitor flow converge.
Read More →
SamTrans Sets Priorities for Potential Connect Bay Area Revenue
The board-approved framework allocates future funding to maintaining service, rider improvements, equity initiatives, and infrastructure repairs.
Read More →
Federal Transit Officials Launch MARTA Safety Probe
FTA has given MARTA 15 days to provide records on crime prevention, fare evasion enforcement, and security funding as part of a broader safety investigation.
Read More →
Strategic Safety Measures at CATS Lead to Drop in Transit Crime
Under the leadership of the CATS Chief Safety and Security Officer, the organization has marked a pivotal transformation.
Read More →
Chicago's NITA Act Moves Into Next Phase as Service Improvements Begin
Rider-focused improvements will begin rolling out across the system immediately as CTA, Metra, and Pace increase service this summer in the six-county region.
Read More →
How Transit Agencies Are Evolving Enforcement-Only Models With Care-Based Safety Strategies
Transit agencies are redefining safety with care-based response models. See how leaders are improving trust and operations.
Read More →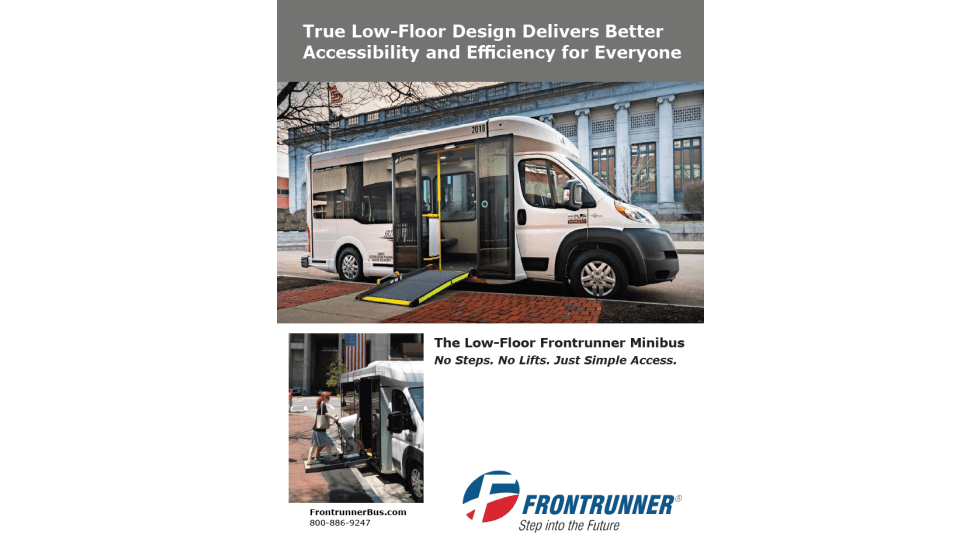
A True Low-Floor Minibus Design Delivers Better Accessibility and Efficiency for Everyone
As transit demands evolve, so should your fleet. Download the whitepaper to see how the Low-Floor Frontrunner Minibus compares to traditional options.
Read More →
WMATA Debuts 'Fares Pay for Service' Awareness Campaign
The campaign was highlighted during a media event at the Paul S. Sarbanes Transit Center in Silver Spring, where WMATA’s GM/CEO Randy Clarke joined Metro Transit Police officers, WMATA management team, board members, and staff to expand fare enforcement and customer education efforts on Metro Bus routes throughout the region.
Read More →
